-
A tale of Phobos - how we almost cracked a ransomware using CUDA
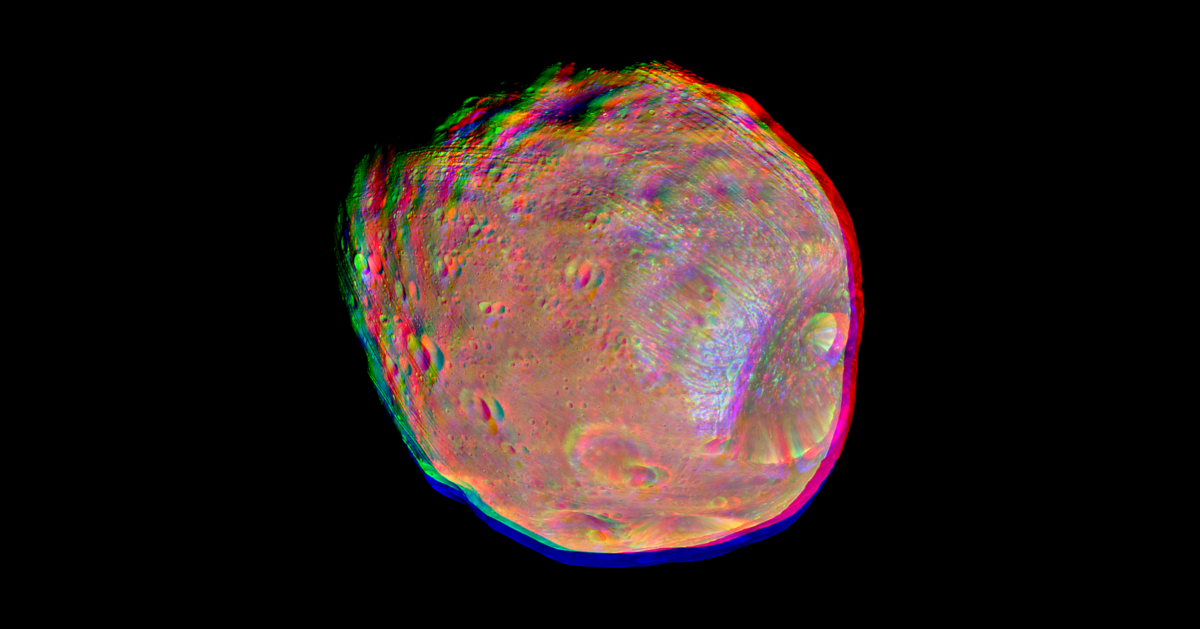
For the past two years we've been tinkering with a proof-of-concept decryptor for the Phobos family ransomware. It works, but is impractical to use for reasons we'll explain here. Consequently, we've been unable to use it to help a real-world victim so far. We've decided to publish our findings and tools, in hope that someone will find it useful, interesting or will continue our research. We will describe the vulnerability, and how we improved our decryptor computational complexity and performance to reach an almost practical implementation.
Read more -
Artemis vulnerability scanner is now open source

The Artemis vulnerability scanner is now open source! Artemis is a tool developed by the CERT Polska team and initiated by the KN Cyber science club of Warsaw University of Technology. The tool is built to find website misconfigurations and vulnerabilities on a large scale. Thanks to its modular architecture, it can combine the results of various other tools in a single place.
Read more -
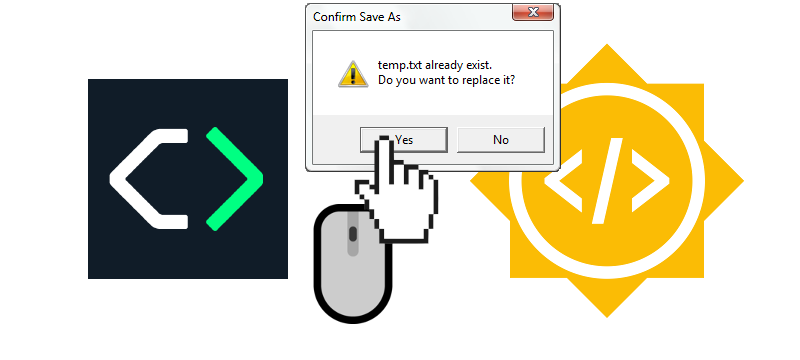
Artemis – CERT Polska verifies the cybersecurity of Polish organizations

The New Year has brought more solutions to improve the security of the Polish Internet. One of them is Artemis, a tool developed by the CERT Polska team and initiated by the KN Cyber science club of Warsaw University of Technology. Artemis was designed to look for websites misconfigurations and vulnerabilities on a mass scale. We use it to verify infrastructure of entities for which, according to the National Cyber Security System Act, incident handling is coordinated by CSIRT NASK.
Read more -
Vidar stealer campaign targeting Baltic region and NATO entities

While working on our automatic configuration extractors, we came across a rather strange-looking Vidar sample. The decrypted strings included domain names of such organizations as the NATO Strategic Communications Centre of Excellence, Border Guard of Poland, Estonia and Latvia, and Ministry of the Interior of Lithuania. Automatically extracted strings from …
Read more -
Linux Injector for automated malware analysis
Guest post by our Google Summer of Code student, Manorit Chawdhry Project proposal: https://summerofcode.withgoogle.com/projects/#6209067233574912 Motivation Wait, what? Malware on Linux? Yup, you read it right. Linux malware isn't given much importance in our community, as Windows is the most targeted operating system for malicious attacks …
Read more -
HID simulation for DRAKVUF
Guest post by our Google Summer of Code student, Jan Gruber Project proposal: https://summerofcode.withgoogle.com/projects/#6703931754807296 Overview My project for GSoC 2021 was to realize an undetectable simulation of human behaviour in the VMI-based sandbox DRAKVUF, which resulted in the contribution of a plugin named hidsim - short …
Read more -
CFP Secure 2021

Why SECURE? Do you value hard work and facing challenges? Do you want to meet people like you, share your job results, look for inspiration or partners to mutual projects? You can find it all in October on our conference. We invite you to contribute to the agenda of the …
Read more -
Karton Gems 3: Malware extraction with malduck

Table of contents Getting Started Your first karton Malware extraction with malduck Introduction Today we'll continue topics started in the first part of the tutorial. We'll learn about malduck, what can it do and how to write your own modules. Later we'll also show how to integrate it with Karton …
Read more -
Karton Gems 2: Your first karton

Table of contents Getting Started Your first karton Malware extraction with malduck Introduction In the last part, we've explained how to set up a simple Karton pipeline and start your tasks. If you haven't already, it's probably a good idea to read it now. Or you can clone the karton-playground …
Read more -
Karton Gems 1: Getting Started

Table of contents Getting Started Your first karton Malware extraction with malduck What is Karton? Karton is a framework for microservice orchestration, designed by security researchers for security researchers (but flexible enough to be used everywhere). It shines in scenarios where there is a clear separation of "input" and "output …
Read more