The Artemis vulnerability scanner is now open source! Artemis is a tool developed by the CERT Polska team and initiated by the KN Cyber science club of Warsaw University of Technology. The tool is built to find website misconfigurations and vulnerabilities on a large scale. Thanks to its modular architecture, it can combine the results of various other tools in a single place.
What is the architecture of Artemis?
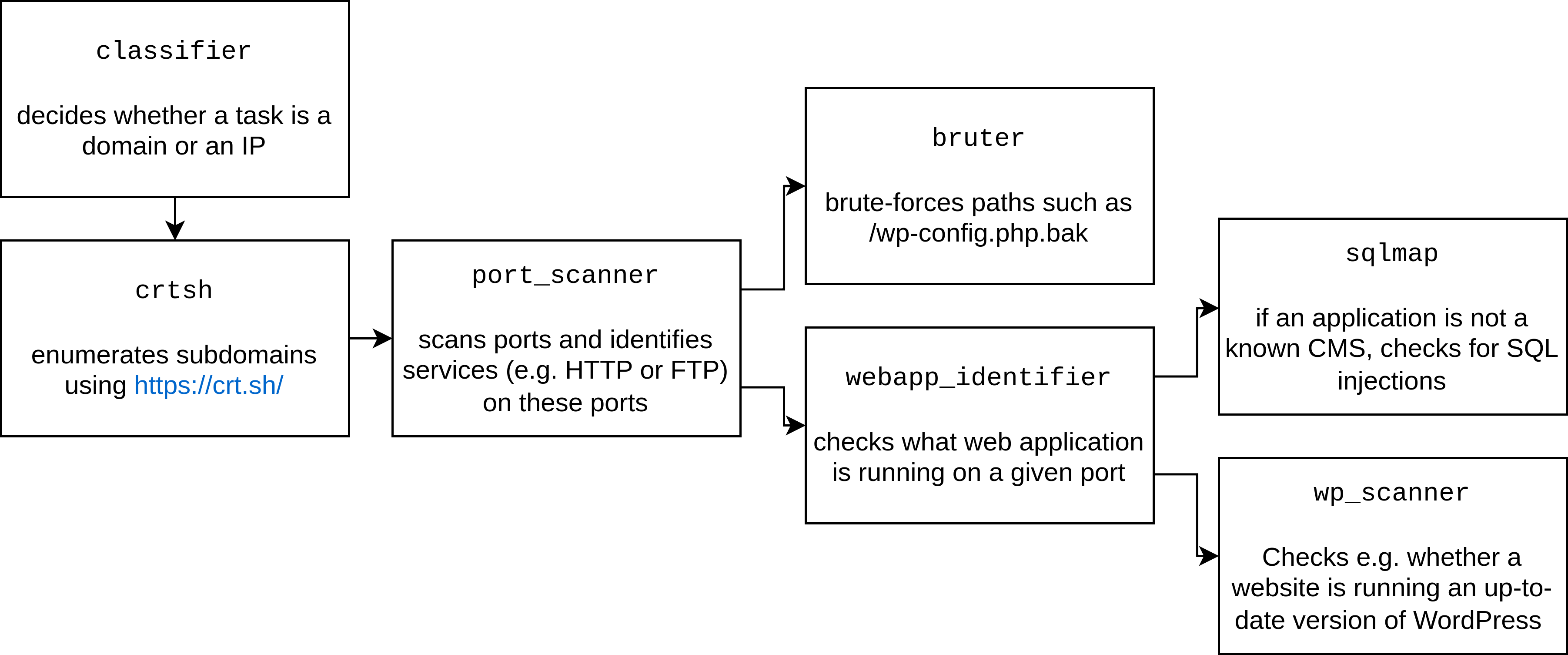
Artemis is based on the Karton framework and various scanning features are implemented by specialized Karton modules. Each module can:
- accept tasks (for example: a domain),
- perform some actions (for example: enumerate subdomains using https://crt.sh/),
- and produce other tasks (for example: produce new subdomains).
This way, the scanning can be:
- decomposed into small tasks that are performed in parallel,
- easily extended with new modules.
The following diagram describes the flow of tasks through a small subset of Artemis modules:
You can view the full list of Artemis modules on:
- https://github.com/CERT-Polska/Artemis/tree/main/artemis/modules (the core modules),
- https://github.com/CERT-Polska/Artemis-modules-extra (the modules that, due to licensing reasons, couldn't have been included in core).
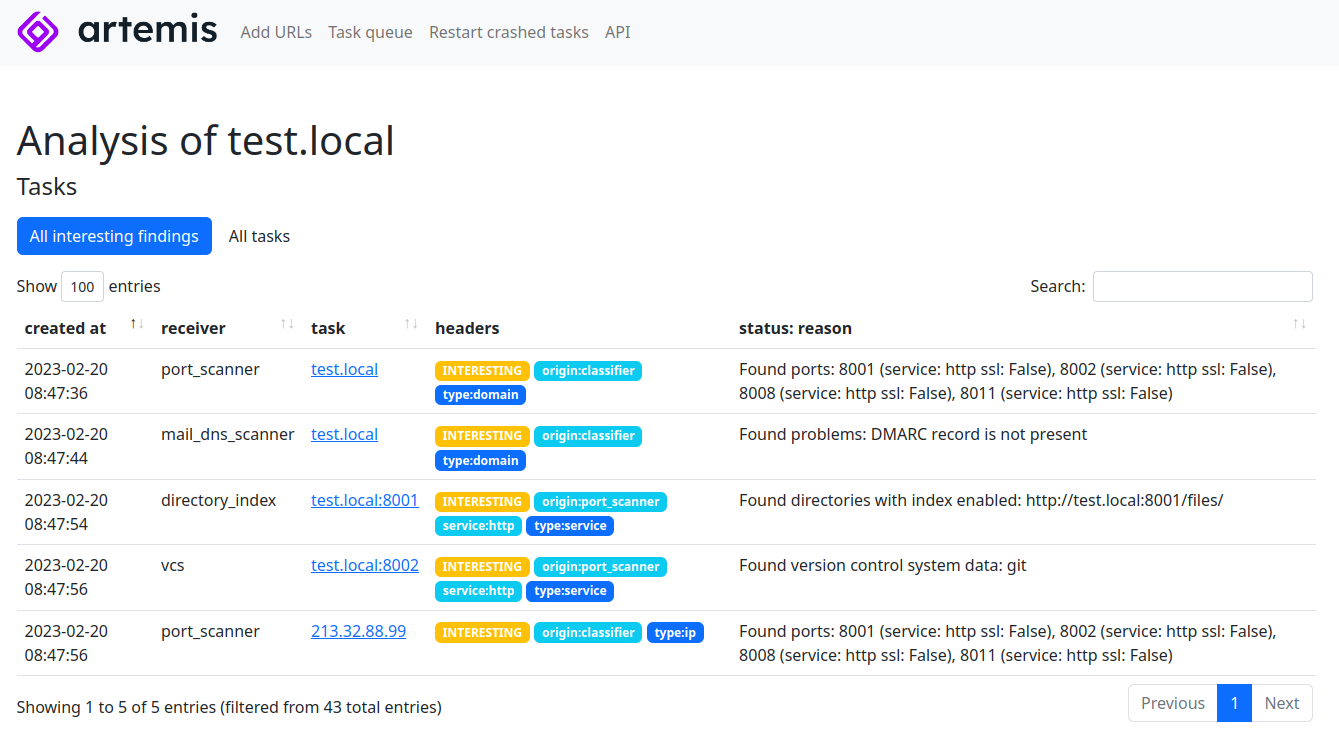
The following screenshot contains an example of Artemis results:
Why have we built it?
We built a custom tool because we wanted to have a tool that:
- can invoke other tools (such as port scanners, Nuclei, sqlmap),
- can be distributed on multiple machines if such a need arises,
- even when running in a distributed way, doesn't overload any single host with requests - the total number of requests per single IP address is limited.
That's why we didn't use any off-the-shelf tools. When possible, we stand on the shoulders of giants other researches and incorporate the results of other tools into Artemis.
How to use it?
To use Artemis, read our quick start guide.
How to help?
Contributions are welcome! We will appreciate both ideas for new Artemis modules (added as GitHub issues) as well as pull requests with new modules or code improvements in our GitHub repository.
